Alternative Network Technologies: Token Ring
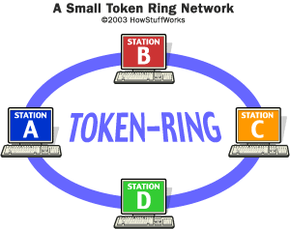
The most common local area network alternative to Ethernet is a network technology developed by IBM, called token ring. Where Ethernet relies on the random gaps between transmissions to regulate access to the medium, token ring implements a strict, orderly access method. A token-ring network arranges nodes in a logical ring, as shown below. The nodes forward frames in one direction around the ring, removing a frame when it has circled the ring once.
- The ring initializes by creating a token, which is a special type of frame that gives a station permission to transmit.
- The token circles the ring like any frame until it encounters a station that wishes to transmit data.
- This station then "captures" the token by replacing the token frame with a data-carrying frame, which encircles the network.
- Once that data frame returns to the transmitting station, that station removes the data frame, creates a new token and forwards that token on to the next node in the ring.
Token-ring nodes do not look for a carrier signal or listen for collisions; the presence of the token frame provides assurance that the station can transmit a data frame without fear of another station interrupting. Because a station transmits only a single data frame before passing the token along, each station on the ring will get a turn to communicate in a deterministic and fair manner. Token-ring networks typically transmit data at either 4 or 16 Mbps.
Advertisement
Fiber-distributed data interface (FDDI) is another token-passing technology that operates over a pair of fiber optic rings, with each ring passing a token in opposite directions. FDDI networks offered transmission speeds of 100 Mbps, which initially made them quite popular for high-speed networking. With the advent of 100-Mbps Ethernet, which is cheaper and easier to administer, FDDI has waned in popularity.