The FBI and Apple spent weeks yelling and screaming at each other over a cell phone, mimicking parents and teenagers everywhere. But the showdown between the government and the maker of iPhones went a lot deeper than some teen Snapchatting at the dinner table. It brought up topics like privacy rights, government overreach and the very real threat of terrorism.
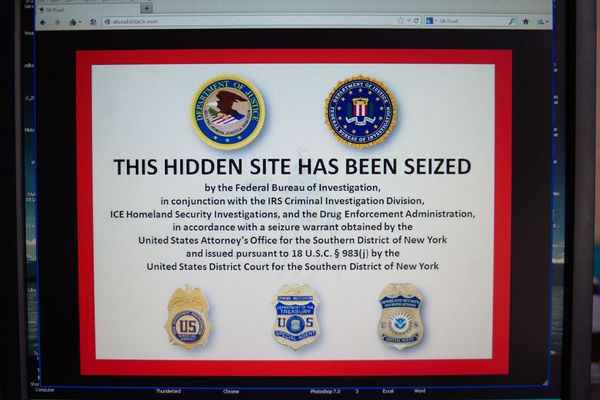
In the end — or at least the end of this chapter — the FBI won, cracking the iPhone (with the help of some real hackers) belonging to one of the shooters in the San Bernardino terrorist attack and gaining access to its data.
Advertisement
The successful break-in brought up even more questions. Who was right? What did the G-men find on the phone? What are they going to do with it? Will they share their break-in methods with anyone else? What's Apple's next move?
The most pressing question, though, might be this: How the heck did they do it?
"Technically ...," says Robert Siciliano, an identity theft expert with BestIDTheftCompanys.com and an expert on mobile phone security, "I don't know. More than likely, we will know. Eventually. And that's the problem. That's the issue that Apple has had with this whole process."
An NBC News report says that an Israeli firm called Cellebrite helped crack the phone for the FBI. And even though its methodology is still secret, the secret is now out: It can be done. And sooner or later, as Siciliano suggests, the word on how to do it will leak out. The FBI already has said it'll help other law enforcement agencies with locked phones.
None of this should be particularly surprising. It's a way of life in the tech world. Engineers build. Hackers break in.
It's just that, usually, it's not the government trying to bust in or demanding someone else open it.
"With every technology, whether it's Microsoft, Android, Apple's iPhone — heck it could be your car, it's your friggin' toaster, your refrigerator,” Siciliano says, "with every technology, there's a way to game it. There's always a way to game it."
And that, of course, may be the moral to this whole 21st-century fable: No matter how secure you think your phone is — or your computer, or your tablet, or your autonomous car — some bad guy somewhere will be looking for a way to make it unsecure.
"The chase is always on,” Siciliano says. “It's never NOT been on."
Technically, the best way to get into any locked tech device is to, well, unlock it. That is, to key in the proper passcode. There are ways to bypass the passcode, to find a flaw in the operating system. They're all over the Interwebs. Some of them may even work.
But the first try is finding the right passcode. Whether that's a matter of coming up with some arcane algorithm that does the job or just making a really good guess hardly matters. Getting there is the thing.
Being savvy 21st-century consumers, though — you know, the kind who have downloaded a game featuring hacked-off birds billions of times — we know how to secure our deepest, darkest secrets, too.
Password protect everything. Use good passwords. Stay off unsecured Wi-Fi networks. Keep your home network safe with good passwords. Don't click on that link from that Saudi princess looking for your help. Don't flash your new tech all over the train. Get security software if you feel you need it. Keep your stuff away from the FBI.
Importantly, don't put anything on your phone or other device that is so sensitive that you never want anyone to see it. Assume worst-case scenario. Assume it will be compromised.
And, more than anything, keep on your toes. Be aware. Make sure your stuff is as safe as can be. That's about all you can do.
"Safety is a process," Siciliano says. "Working in a factory, you don't just all the sudden be safe and take your safety glasses off and your hardhat off. You're in a factory. It's an ongoing process of being safe.
"It's the same thing with technology. There's always going to be someone that wants more access, for whatever reason. Because they're just curious or inventive or they're a criminal or they just want to be able to profit. There's no such thing as 100 percent safety or security, ever. And there never will be."
So it's time to change-up that passcode again and get rid of those embarrassing selfies. And do it quickly. Before the FBI shows up.
Advertisement