Spam Distribution
Spam continues to be a huge problem. It's a frustrating experience to open your e-mail and sort through dozens of examples of junk mail. Where does all that spam come from? According to FBI estimates, a large percentage of it comes from networked zombie computers.
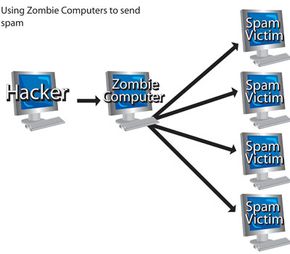
If spam came from one centralized source, it would be relatively easy to track it down and either demand the corresponding ISP shut down that computer's access to the Internet or charge the user for sending out illegal spam. To get around these pitfalls, crackers rely on zombie computers. The zombie computer becomes a proxy, meaning the cracker is one step removed from the origin of spam e-mails. A cracker with a large botnet can send millions of spam messages every day.
Advertisement
Crackers might set up a spam botnet to deliver a computer virus or Trojan program to as many computers as possible. They also can use spam to send phishing messages, which are attempts to trick users into sharing personal information (we'll talk more about phishing later).
When sending out ads in spam mail, the cracker either sets up the botnet specifically for a client or he rents it out on an hourly basis. Clients who wish to advertise their products (and who don't care how intrusive or illegal their advertisements might be) pay the crackers to send out e-mail to thousands of people.
The majority of e-mail recipients usually can't figure out where the spam is coming from. They might block one source only to receive the same spam from a different zombie in the botnet. If the e-mail includes a message that says something like "Click here to be removed from this e-mail list," they might fall prey to exposing their computer to even more spam. Users savvy enough to track the e-mail back may not notice that the sender's computer is part of a larger network of compromised machines. For someone who knows what he's doing, it's not always impossible to figure out if a sender is a single user sending out spam or if a cracker is controlling the computer remotely. It is, however, time consuming.
A zombie-computer owner might realize a cracker is controlling his machine remotely if spam recipients write to complain about the junk mail or if his own e-mail outbox is full of messages he didn't write. Otherwise, the owner is likely to remain blissfully unaware that he's part of a ring of spammers. Some users don't seem to care if their machines are being used to spread spam mail as if it were someone else's problem and many more don't take the necessary precautions to avoid becoming part of a botnet.
In the next section, we'll talk about another vicious use of botnets -- distributed denial of service attacks.