Distributed Denial of Service Attacks
Sometimes a cracker uses a network of zombie computers to sabotage a specific Web site or server. The idea is pretty simple -- a cracker tells all the computers on his botnet to contact a specific server or Web site repeatedly. The sudden increase in traffic can cause the site to load very slowly for legitimate users. Sometimes the traffic is enough to shut the site down completely. We call this kind of an attack a Distributed Denial of Service (DDoS) attack.
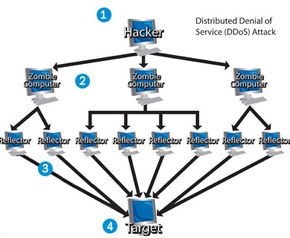
Some particularly tricky botnets use uncorrupted computers as part of the attack. Here's how it works: the cracker sends the command to initiate the attack to his zombie army. Each computer within the army sends an electronic connection request to an innocent computer called a reflector. When the reflector receives the request, it looks like it originates not from the zombies, but from the ultimate victim of the attack. The reflectors send information to the victim system, and eventually the system's performance suffers or it shuts down completely as it is inundated with multiple unsolicited responses from several computers at once.
Advertisement
From the perspective of the victim, it looks like the reflectors attacked the system. From the perspective of the reflectors, it seems like the victimized system requested the packets. The zombie computers remain hidden, and even more out of sight is the cracker himself.
The list of DDoS attack victims includes some pretty major names. Microsoft suffered an attack from a DDoS called MyDoom. Crackers have targeted other major Internet players like Amazon, CNN, Yahoo and eBay. The DDoS names range from mildly amusing to disturbing:
- Ping of Death - bots create huge electronic packets and sends them on to victims
- Mailbomb - bots send a massive amount of e-mail, crashing e-mail servers
- Smurf Attack - bots send Internet Control Message Protocol (ICMP) messages to reflectors, see above illustration
- Teardrop - bots send pieces of an illegitimate packet; the victim system tries to recombine the pieces into a packet and crashes as a result
Once an army begins a DDoS attack against a victim system, there are few things the system administrator can do to prevent catastrophe. He could choose to limit the amount of traffic allowed on his server, but this restricts legitimate Internet connections and zombies alike. If the administrator can determine the origin of the attacks, he can filter the traffic. Unfortunately, since many zombie computers disguise (or spoof) their addresses, this isn't always easy to do.
In the next section we'll look at some other ways crackers use zombie computers.