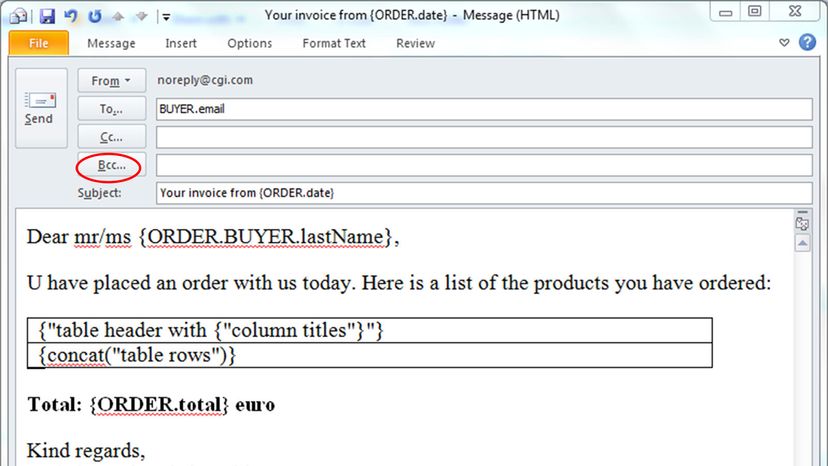
Your typical email program has several options to simultaneously message more than one person. You can load up the "To" box with many recipients and then blast away. Or you can put some (or one) in the "To" spot and CC the rest. Or else BCC some or all.
The BCC might be the trickiest as it means that not everyone is privy to the same information. And it has the biggest risk for pitfalls. So, when do you CC and when do you BCC?
Advertisement
First, you have to know what CC and BCC mean. The CC field stands for carbon copy; the BCC field stands for blind carbon copy. Carbon copies were common in pre-internet days. When someone needed a copy of a document, they inserted a sheet of carbon paper between two pieces of paper. The carbon paper helped the ink or type move from the top sheet to the bottom, and presto, you had two copies of the same paperwork.
What does cc mean in email? These days, an email CC means you sent a copy of a message to someone other than the direct recipient – it's an easy way to keep vested parties in the loop on a subject. Notably, the CC format allows everyone to see each other's email addresses, too.
BCC works the same way as CC, except the direct recipient (in the "To" line) doesn't know that anyone was copied on the message. So, for example, if you emailed a subordinate at work about being late to the office and BCC'd your own boss to show her that you were being diligent about tardiness, your subordinate wouldn't know that her lateness was being pointed out to your own superior.
Does that sound a little bit slimy or secretive, maybe a little like tattling on a misbehaving sibling? It should. You could call BCC the "backstabbing carbon copy," because its usage is often loaded with etiquette pitfalls and potential backlash. After all, if you're purposely hiding the fact that there are BCC recipients, maybe you should question your motives.
BCC is a notorious office space landmine, particularly if the person who is BCC'd accidentally hits Reply All. Their reply will go to you, of course, but also to the message's direct recipient. Whoops. This kind of abrupt disclosure has resulted in countless tense office scenarios. The takeaway? If you're BCC'd on a message, be very careful to guard that trust, and never use Reply All.
In spite of these issues, there are some very good reasons to use BCC. Maybe you're a supervisor of various contract or freelance workers who never interact with each other, and you want to update all of them on policy changes without having to send individual emails. To do so, you can send them all a message with just the BCC section filled in with their addresses.
This isn't just a matter of convenience for you – it also protects the privacy of your freelancers, who probably don't want a bunch of virtual strangers to see their personal email address.
Or maybe you're a company trying to contact many customers about an important issue. You absolutely have to use BCC, otherwise hundreds or thousands of people will suddenly see private email addresses. That's a major breach of trust.
Advertisement


