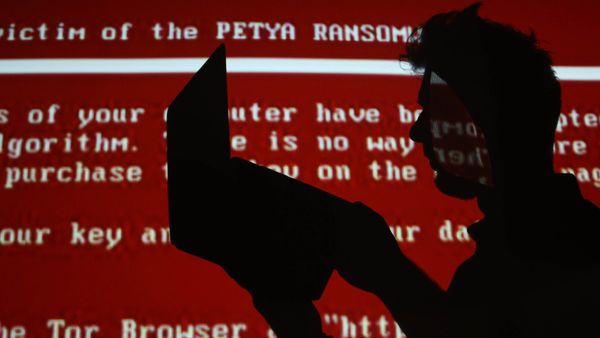
In March 2018, Atlanta was hit with a ransomware attack that infected nearly 3,800 government computers belonging to the city of Atlanta, including servers. After the virus was deployed, the ransomware essentially locked all the infected computers, rendering them impossible to access. Atlanta's court system went down; police were unable check license plates; residents couldn't pay bills online.
Just three weeks before Atlanta was hit, the small city of Leeds, Alabama, also experienced an identical cyberattack. And before Leeds in January, it was Hancock Regional Hospital in the suburbs of Indianapolis.
Advertisement
What these three attacks have in common is they were all hit by SamSam ransomware, also known as MSIL/Samas.A. Each attack demanded around the same amount — about $50,000 in cryptocurrency. Hancock Regional Hospital and Leeds, Alabama, paid the ransom. However, the city of Atlanta did not. Instead, it chose to pay millions to get its systems back online.
At that time, the city of Atlanta was one of the most prominent to be attacked by ransomware, which according to John Hulquist, is when a cybercriminal accesses a network of computers, encrypts all the data and extorts the company to unlock it. Hulquist is vice president of analysis, Mandiant Threat Intelligence at FireEye, an intelligence-led security company.
Advertisement