Encryption is the process of encoding data so that only a computer with the right decoder will be able to read and use it. You could use encryption to protect files on your computer or e-mails you send to friends or colleagues. An encryption key tells the computer what computations to perform on data in order to encrypt or decrypt it. The most common forms of encryption are symmetric-key encryption or public-key encryption:
- In symmetric-key encryption, all computers (or users) share the same key used to both encrypt and decrypt a message.
- In public-key encryption, each computer (or user) has a public-private key pair. One computer uses its private key to encrypt a message, and another computer uses the corresponding public key to decrypt that message.
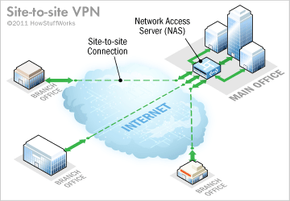
In a VPN, the computers at each end of the tunnel encrypt the data entering the tunnel and decrypt it at the other end. However, a VPN needs more than just a pair of keys to apply encryption. That's where protocols come in. A site-to-site VPN could use either internet protocol security protocol (IPSec) or generic routing encapsulation (GRE). GRE provides the framework for how to package the passenger protocol for transport over the internet protocol (IP). This framework includes information on what type of packet you're encapsulating and the connection between sender and receiver.
IPSec is a widely used protocol for securing traffic on IP networks, including the internet. IPSec can encrypt data between various devices, including router to router, firewall to router, desktop to router, and desktop to server. IPSec consists of two sub-protocols which provide the instructions a VPN needs to secure its packets:
- Encapsulated Security Payload (ESP) encrypts the packet's payload (the data it's transporting) with a symmetric key.
- Authentication Header (AH) uses a hashing operation on the packet header to help hide certain packet information (like the sender's identity) until it gets to its destination.
Networked devices can use IPSec in one of two encryption modes. In transport mode, devices encrypt the data traveling between them. In tunnel mode, the devices build a virtual tunnel between two networks. As you might guess, VPNs use IPSec in tunnel mode with IPSec ESP and IPSec AH working together [source: Friedl].
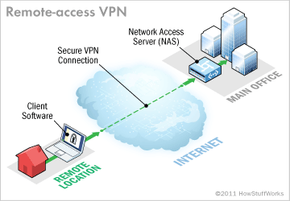
In a remote- access VPN, tunneling typically relies on Point-to-point Protocol (PPP) which is part of the native protocols used by the internet. More accurately, though, remote-access VPNs use one of three protocols based on PPP:
- L2F (Layer 2 Forwarding) — Developed by Cisco; uses any authentication scheme supported by PPP
- PPTP (Point-to-point Tunneling Protocol) — Supports 40-bit and 128-bit encryption and any authentication scheme supported by PPP
- L2TP (Layer 2 Tunneling Protocol) — Combines features of PPTP and L2F and fully supports IPSec; also applicable in site-to-site VPNs
Throughout this article, we've looked at the types of VPNs and the components and protocols that they use. Over time, people have developed new and better technologies to use in networks, which improves the features of existing VPNs. VPN-specific technologies, though, such as tunneling protocols, haven't changed much in that time, perhaps because current VPNs do such a good job at to keep businesses connected around the world. Tunnel on to the next page for lots more information about virtual private networks.