The days of relying on an ethernet cable are over! Routers have undergone significant evolution over the past few years, driven by the relentless demand for faster internet speeds, greater range, and more reliable connections. Modern wireless routers have transcended the basic functionality of merely connecting devices to the internet.
Today, they are equipped with advanced features such as dual-band or even tri-band capabilities, allowing them to broadcast on multiple frequencies simultaneously. This advancement reduces interference and increases the capacity to support more devices without compromising the quality of connection.
Faster Internet Access
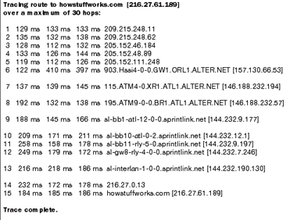
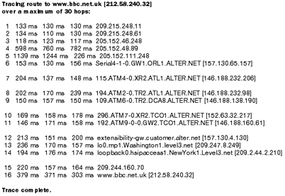
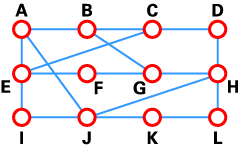
Packet switched networks for your multiple devices are more dynamic than ever. The adoption of the latest Wi-Fi standards, such as Wi-Fi 6 (802.11ax), marks a pivotal shift in wireless network technology. Wi-Fi 6 routers offer faster data rates, increased capacity, and improved performance in environments with many connected devices, along with better power efficiency for devices.
Additionally, the integration of Mesh network technology in wireless routers has revolutionized the home network. By seamlessly connecting multiple router nodes to blanket a home with Wi-Fi coverage, Mesh systems ensure there are no dead zones, providing a consistent and strong Wi-Fi signal throughout larger homes.
Tougher Network Security
The evolution of wireless routers also reflects in their enhanced security features. With the rise in cybersecurity threats, modern routers now come with robust security protocols such as WPA3, which provides cutting-edge encryption.
Furthermore, many routers now include built-in VPN support, parental controls, and the ability to manage network access through mobile apps, making network management more accessible and comprehensive for the average user. This evolution not only reflects technological advancement but also a shift towards more user-centric designs, accommodating the increasing reliance on connected devices in daily life.
For more information on routers and related topics, check out the links on the next page.
This article was updated in conjunction with AI technology, then fact-checked and edited by a HowStuffWorks editor.