Log in to your e-mail account. Log in to your bank account. Log in to Facebook. Log in to your Amazon account. Log in to your photo sharing service. Can you count the number of applications you use on a regular basis that require a password? This includes your local computer account, your e-mail, social networking Web sites and merchant accounts at various online stores. If you're in school or at work, you should count password-protected resources you use there, too, like your personal records or network file shares. How do you keep track of all of all those passwords?
Here are a few tricks you might have tried or considered (with hints about why you may want to steer clear of some of them):
Advertisement
- Memorize passwords. This is a great technique if you use your passwords every day, but maybe not for those you only need occasionally. If you don't use a password regularly, there's a good chance you could forget it if you rely on memorization alone. In addition, Web browser cookies can remember your login session for days or weeks at a time, meaning you only enter the password manually once in a while even if you use it every day.
- Use the same password everywhere. Memorizing a single password for every account does make life simpler. For security reasons, though, this isn't a great idea, because it makes it easy for a hacker who finds your user name and password for one account to break into your other accounts, too.
- Write passwords down on paper. This is an ideal solution if you can hide the written information where no one else has access. Not only is this a risk if someone finds the list, but a written list or an assortment of scraps of paper could also be lost or damaged, and you'll need to find and update the list each time you update a password.
- Write passwords into a file on your computer or mobile device. This is less likely to get lost than the paper, but you do risk losing the file if you have hardware failure. In addition, this file is as vulnerable to hackers as other files on your computer. You could encrypt it for an added layer of security, which makes this strategy similar to the next solution.
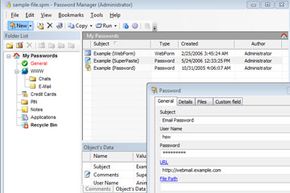
- Use password management software. Password management software is a utility you can use to save and retrieve all your passwords. This software could be a standalone application on your local computer or a feature within another application. This option greatly limits hackers' possible routes to your password data while adding convenient features for organizing and retrieving information.
In this article, we're going to break down the types of password management software, and we'll examine both the benefits and the risks of using each type. We'll also discover some specific applications on the market and sort out which ones are hit-or-miss in both features and security. But first, a walk down password management software's memory lane as we look at its history.
Advertisement