Key Takeaways
- Spyware is illegal software installed without a user's consent to monitor or control their computer activity, often leading to performance degradation and privacy breaches.
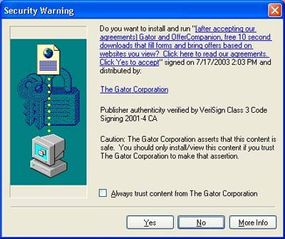
- Protection against spyware includes using antivirus tools with spyware scanning features, enabling pop-up blockers and being cautious about allowing software installations from the internet.
- Legal frameworks like the Computer Fraud and Abuse Act and various state laws combat spyware, but enforcement can be challenging due to the difficulty in tracing spyware back to its originators.
Has your computer ever become so slow that you can fix yourself a snack in the time it takes your word processor to open? Perhaps spyware is to blame.
Spyware is a category of computer programs that attach themselves to your operating system in nefarious ways. They can suck the life out of your computer's processing power. They're designed to track your Internet habits, nag you with unwanted sales offers or generate traffic for their host Web site. According to some estimates, more than 80 percent of all personal computers are infected with some kind of spyware [source: FaceTime Communications]. But before you chuck your computer out the window and move to a desert island, you might want to read on. In this article we'll explain how spyware gets installed on your computer, what it does there and how you can get rid of it.
Advertisement
Some people mistake spyware for a computer virus. A computer virus is a piece of code designed to replicate itself as many times as possible, spreading from one host computer to any other computers connected to it. It usually has a payload that may damage your personal files or even your operating system.
Spyware, on the other hand, generally isn't designed to damage your computer. Spyware is defined broadly as any program that gets into your computer without your permission and hides in the background while it makes unwanted changes to your user experience. The damage it does is more a by-product of its main mission, which is to serve you targeted advertisements or make your browser display certain sites or search results.
At present, most spyware targets only the Windows operating system. Some of the more notorious spyware threats include Trymedia, Nuvens, Estalive, Hotbar and New.Net.Domain.Plugin [source: CA].
Advertisement