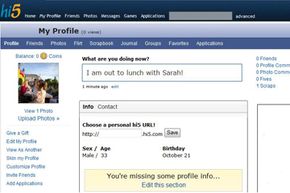
Social networking sites are getting bigger and better every day, but if you don't find Facebook and MySpace to your liking, you have plenty of other options. One of the most popular is Hi5. Hi5 shares many similarities with social network sites that are already household names, but it introduces some twists that make it worthwhile for people who love trying out new and interesting online communities.
Hi5 bears more than a passing visual resemblance to other social networking sites. It also shares statistical parallels with MySpace and Facebook; all three are among the top 25 most-visited Web sites in the world [source: Comscore]. That may surprise you if you live in the United States and you haven't heard of Hi5 before. But there's a good reason for that: Ramu Yalamanchi founded the site in 2003, and he purposely focused building a membership base in countries other than the United States, in part to avoid struggling against its well-established competitors.
Advertisement
That strategy seems to be serving Hi5 very well. The site now claims around 60 million members from more than 200 countries, and tellingly, the majority of those members aren't from the United States [sources: Hi5, TechCrunch].
In addition to stressing its expansion in other countries, Hi5 is deploying other tactics to attract new members. One of the site's biggest transformations is the addition of many entertainment options, primarily in the form of games. Members can select from a huge slate of online or downloadable games. Many of those games are free, while others, like those from name-brand game supplier RealNetworks, require payment.
So whether you're looking for a posse of new friends or want to unwind with some fun games, Hi5 is becoming a top online destination. Keep reading to see how you can get the most of this burgeoning online community.
Advertisement