Computer Security Systems
Computer security is an increasingly important consideration. From authentication to encryption keys, learn how to keep your computer's hard drive protected and your personal information safe.
Learn More / Page 2
Online harassment seems to know no bounds, with new opportunities for meanness evolving all the time. Ever heard of dogpiling or doxing?
By Alia Hoyt
Remember that crazy video you made with your friends years ago? Yes, you do, but you also wish it wasn't the first thing that pops up in a Google search of your name. Well, rejoice! There's a way to get it out of Google.
By Beth Brindle
Do you know what you're doing when you're "dropping dox" on somebody? It's called "doxxing," and while it's technically not illegal, it's probably not a very nice thing to do to someone.
By Beth Brindle
Advertisement
You've probably heard of the hacktivist group known as Anonymous, but do you really know what motivates the group's actions or how members organize their initiatives?
The entertainment industry has tried to stop people from making digital copies of its work, but in 2011, they enlisted the help of the U.S. government. What is the Stop Online Piracy Act and what would it achieve?
Tracking copyrighted files online is a tricky business, but cutting-edge software has learned to recognize data unique to music and movie clips. You're also leaving digital traces of yourself all over the internet. How are these two things related?
No one should think of surfing the Internet without some kind of anti-virus software protection. Learn if there is any free anti-virus software in this article.
Advertisement
Millions of people around the world have personal profiles on social networking sites. But when those people pass away, what happens to all that personal information they put online?
What does it take to cripple a nation? Someone with solid computer skills, for a start. Nefarious hackers wield a lot of power with a few keystrokes, and the United States is taking action.
We all get spam e-mail messages that tell us to follow a link. But that link could download a Trojan horse. What is it, and how is it different from a virus?
By John Fuller
Sometimes it seems like no matter what internet community you join, someone's trying to drive you crazy. Are they just annoying or are they trolling?
Advertisement
Hackers can disable digital infrastructure in minutes. Is it only a matter of time before countries attack one another's computers? Or have they already started?
Most computer-savvy people know about viruses and how to prevent an infection. But what are some of the most destructive viruses of all time, the record-smasher server-crashers?
People traveling to the United States have grown accustomed to tight security. But can the government really take your laptop and keep it indefinitely?
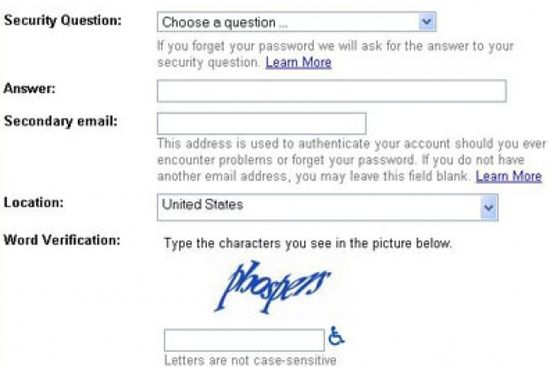
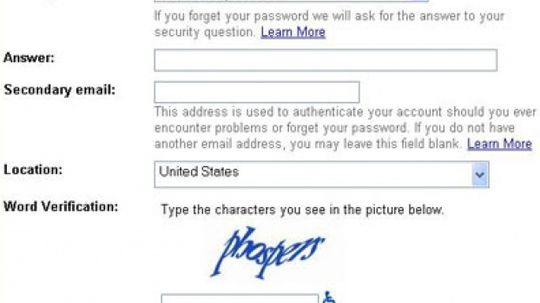
Are you a computer? If you've ever successfully filled in a CAPTCHA on the Web, you're probably not. So what is this test, and what does it do?
Advertisement
Digital signatures make sure the documents you send electronically are authentic. Learn about digital signatures and other authentication methods.
Could your e-mail be used against you in a court of law? Maybe. Computer forensics searches, preserves and analyzes information on computer systems for potential evidence in a trial.
Internet censors range from parents and employers to national governments. They block access to the Web pages they identify as undesirable.
E-mail scams are often well-disguised and can be very dangerous. Check out some examples of e-mail scams in this article.
By Tim Crosby
Advertisement
Without hackers, we'd have no PCs or iPods. Yet, hackers have gotten a bad reputation as criminals of the computer age. Are they friends or foes?
As the famous cartoon has it, "On the internet, nobody knows you're a dog." Online fraud is one of the fastest-growing crimes -- so how can you protect yourself?
By Joe Wallace
With the evolution of the internet, the big kid in class who used to steal your lunch money now hacks your e-mail, sends you threatening messages, and sabotages your computer. If you're wondering how to stop cyberbullying, read on!
When hackers take over computers to do their Internet bidding, they create zombie computers. Allegedly, one hacker under investigation used a single computer to control a network of more than 1.5 million zombie computers.
Advertisement
In "Live Free or Die Hard," Detective John McLane fights a group that carries out attacks using the Internet. Is it really possible for hackers to cause economic or physical devastation in the United States?
How did hackers exploit four different "zero day" flaws in Microsoft Word? Find out what went wrong with Microsoft Word.
By Julia Layton